ThreatDown Ultimate Bundle
Conçu pour les organisations aux ressources limitées, ThreatDown Ultime offre une protection complète dans une solution unique qui offre une facilité d'utilisation inégalée à un prix raisonnable.
L'offre groupée ThreatDown Ultimate Bundle comprend les éléments suivants
Gestion de la détection et de la réponse
Surveillance 24 heures sur 24, 7 jours sur 7 et 365 jours par an par les experts de ThreatDown, qui analysent les menaces, y répondent et y remédient en votre nom (même celles qui échappent à la détection technologique).
Rétrospective sur 31 jours
Rétrospective sur 31 jours par l'équipe d'experts de ThreatDowns, qui recherche des indicateurs de compromission afin d'arrêter les attaques et d'affiner les détections et les alertes à l'avenir.
Protection des points finaux et réponse
Solution primée qui fournit une détection et une réponse actives continues, une surveillance des activités suspectes, un bac à sable intégré dans le nuage, une isolation des points d'extrémité, un rollback des ransomwares, une cartographie MITRE ATT&CK et un shell de réponse active.
Gestion de la chasse aux menaces
La chasse aux menaces automatisée et proactive met en corrélation les alertes et les notifications de l'EDR avec les flux de renseignements sur les menaces externes et internes, en donnant la priorité à toutes les alertes et en ne faisant remonter que les plus critiques, avec des conseils de réponse clairs, étape par étape.
Protection des points finaux
Prévention multi-vectorielle reposant sur des couches technologiques qui arrêtent les attaques basées sur des signatures, sans fichier et de type "zero-day" avant qu'elles ne s'infiltrent dans vos systèmes.
Réponse aux incidents
Construit sur le moteur de liaison propriétaire de ThreatDown, il ne se contente pas de supprimer les exécutables des logiciels malveillants, mais trouve et éradique automatiquement tous les fichiers associés et les modifications afin d'empêcher toute réinfection.
Évaluation de la vulnérabilité
Exécutez des analyses à la demande ou selon un calendrier précis pour rechercher les vulnérabilités des systèmes d'exploitation et des applications.
Bloc d'application
Bloquer facilement les programmes non autorisés afin d'appliquer les politiques d'utilisation acceptable.
Filtrage du contenu des sites web
Amélioration de la sécurité et de la productivité en restreignant l'accès à des catégories entières de sites web, à savoir les sites malveillants et les sites indésirables qui ne respectent pas le code de conduite des employés
Une sécurité qui s'améliore
Sur la base des enseignements tirés, l'équipe d'experts de ThreatDowns affine les techniques de sécurité pour des détections et des alertes plus rapides et plus précises au fil du temps.
Pour une analyse détaillée de ce qui est inclus dans l'offre ThreatDown Ultimate, veuillez consulter la page d'accueil de ThreatDown Ultimate. Fiche technique ultime ou vous pouvez comparer toutes les offres groupées de ThreatDown.
Pour une analyse détaillée de ce qui est inclus dans l'offre ThreatDown Ultimate, veuillez consulter la page d'accueil de ThreatDown Ultimate. Fiche technique ultime ou vous pouvez comparer toutes les offres groupées de ThreatDown.

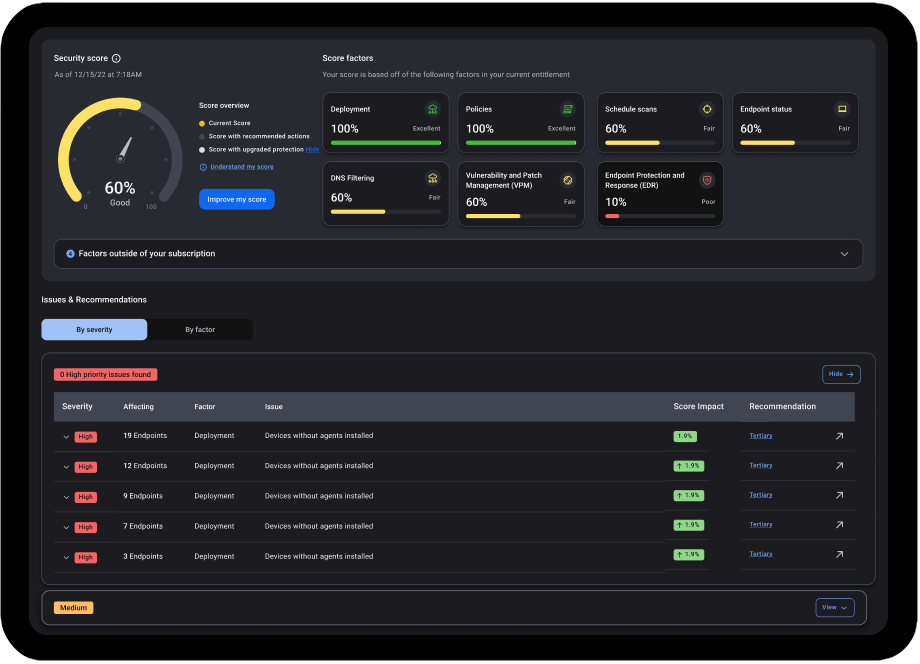
Améliorer la sécurité
Surveillance des points d'accès et réponse 24x7x365 par l'équipe d'experts en cybersécurité de ThreatDowns, qui compte 150 ans d'expérience collective dans la chasse aux menaces, l'analyse médico-légale et la réponse aux incidents.
Détection des attaques grâce à une technologie primée qui comprend la surveillance des activités suspectes, la chasse aux menaces en forme libre et la récupération des rançongiciels (Ransomware Rollback)
Réponse accélérée grâce à une technologie en instance de brevet qui analyse en permanence les alertes et ne transmet que les plus critiques, accompagnées de conseils clairs sur les actions recommandées.
Prévention des menaces avec une protection multi-vectorielle qui ne ralentit pas vos appareils
Réduction de la surface d'attaque avec des processus d'analyse des vulnérabilités et d'application de correctifs qui s'exécutent de manière programmée ou ad hoc, ainsi que le blocage d'applications pour empêcher l'exécution d'applications malveillantes et non désirées.
Blocage de l'application empêcher l'exécution de programmes non autorisés sur les terminaux
Amélioration de la sécurité et de la productivité en restreignant des catégories entières de sites web

Réduire la complexité
Gestion centralisée via une console basée sur le cloud avec une interface conviviale
Un seul agent léger qui se déploie en quelques minutes et fonctionne avec tous les produits ThreatDown
Visibilité des appareils avec des codes de couleur pour un état de sécurité immédiat
Assainissement automobile par le biais d'un moteur de liaison exclusif qui détecte et supprime automatiquement les artefacts, les changements et les altérations de processus
Centre d'opérations de sécurité (SOC) dans une boîte avec les technologies ThreatDown gérées par des experts pour renforcer les efforts de votre équipe

Maximiser la valeur
Mise en œuvre la plus rapide validée par l'indice de mise en œuvre G2 Fall 2023, qui montre que notre suite a le délai de mise en œuvre le plus court de toutes les solutions concurrentes
Plus facile à gérer validé par le G2 Fall 2023 Usability Index, qui a décerné à notre suite la mention “Easiest to use” (la plus facile à utiliser) pour sa facilité d'administration et d'utilisation
Meilleur retour sur investissement validé par le G2 Fall 2023 Results Index, qui a décerné à notre suite le “Meilleur ROI estimé” de toutes les solutions concurrentes
Meilleur rapport qualité-prix pour une offre, un agent, une console et un partenaire de confiance
Pour plus d'informations sur ThreatDown Ultimate et les autres offres groupées disponibles, veuillez nous contacter.
Prendre contact





















 Articles de la base de connaissances
Articles de la base de connaissances