New Product Alert: Introducing ThreatDown ITDR
Blog by Daniella Smith | Posted on Tuesday May 5 2026

Introducing ThreatDown ITDR
Most breaches start with credentials. Stop them there.
Cyber threats have evolved. Today, many breaches don’t rely on traditional hacking methods — instead, attackers use stolen credentials to log in undetected. This allows them to bypass identity protections like IAM and MFA, often leaving little to no visibility into what happens after access is granted.
This is exactly the gap that ThreatDown ITDR is designed to address.
Launching May 4, ThreatDown ITDR is built directly into the existing ThreatDown platform. There’s no need for additional consoles, vendors, or complex integrations.
Join ThreatDown’s Upcoming Webinar
ThreatDown is hosting a webinar on Thursday, May 14 at 4:00 PM (UK time) to demonstrate how ITDR works in practice.
In this session, you’ll learn:
- Today’s threat landscape — and how attackers target identities
- Why ITDR is essential for modern security
- Live demo: how ITDR detects and responds in real time
- What’s next for ThreatDown: product roadmap and innovation
Secure your place today and see how ThreatDown can improve your endpoint security.
Register now to reserve your spot
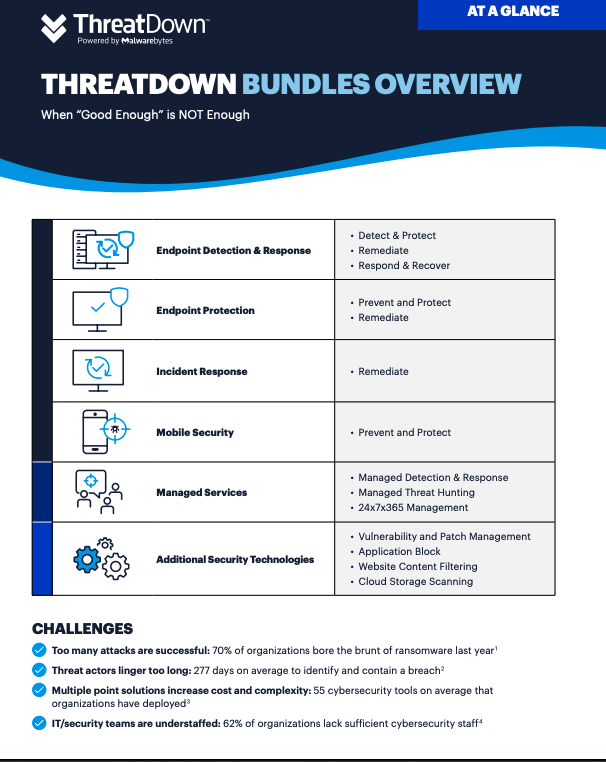
Register nowIntroducing ThreatDown Bundles
A new chapter for Malwarebytes business solutions. Four feature-rich security bundles.

Find out more in our ThreatDown section to see more about the new product bundles, and get in touch.
Get in touch